I do a ton of presenting and have found Keynote on my iPad to be a tremendous upgrade over PowerPoint.
- There's no waiting for boot-up,
- Transitions are beautifully fluid,
- Animations and videos are 100% reliable and always smooth (and never a black box on the screen where a video is supposed to be!),
- Projector compatibility is untouchable, and
 |
Courtesy Geekwire's excellent article, "Undeterred
by Office for iPad, Apple updates iWork suite" |
- Integrated presentation tools such as virtual "crayons" and "laser pointers" mean you never have to face away from your audience.
In a competitive environment, Keynote is a valuable arrow to have in your quiver. Plus, the software runs identically on my iPhone, meaning I can always have your presentations in my pocket. Being able to whip out a compelling, good-looking presentation at a moment's notice conveys a valuable message of preparedness and professionalism. That is not of merely academic merit-- it has meant actual, substantial sales for me.
Keynote presentations also transport reliably. There are none of the missing-font and misplaced-video issues that have afflicted PowerPoint for two decades. With Keynote, all media and other resources are bundled together in an amalgamated file format.
However, the locked-down nature of iOS presents obstacles to sharing Keynote presentations with colleagues. You can store a presentation in iCloud and share a link to that, but if the presentation is large, chances are excellent that the download into the recipient's device will break at some point. Perhaps that will improve over time.
iOS also pioneered a concept of hiding the device's file system, having applications own and manage their own files instead. There is nothing like a Windows Explorer or Finder in iOS. You open Keynote; your Keynote files are right there.
A mysterious option
First, let's agree that using iTunes to convey files from device A to device B is not acceptable in this day and age. Next, let's stipulate that iCloud's current file-conveyance capabilities aren't yet industrial-class, especially with larger Keynote presentations.
But there's a third mechanism: the mysterious WebDAV option you may have noticed in Keynote and other iOS apps, both on iPad and iPhone.
 Web Distributed Authoring and Versioning
Web Distributed Authoring and Versioning is a standards-based approach for making the web a readable and writeable medium. It provides a web-centric, firewall-friendly way of accessing and storing files across the Internet. Sounds good... but, it's not clear what even the first step should be for leveraging this technology on iOS.
First, fond as I am of Dropbox, it does not support WebDAV, and per their FAQs
they have no plans to do so. So it's not a solution here. There are third-party services such as
DropDAV that you can subscribe-to that provide WebDAV compatibility for Dropbox, but for my occasional usage the annual cost seemed unreasonable, and some users would be justifiably uncomfortable with allowing a third-party service to have access to their Dropbox'd files.
A few competing cloud storage providers provide rudimentary WebDAV compatibility, but flaws abound.
Box.net, for example, lets you upload and download using WebDAV-- but with a catch: At least for the pricing tiers I explored, you have to
give your account username and password to anyone you want to be able to access any file. That's such an obvious non-starter that it's almost mind-blowing. Even more mind-blowing is how universal it seems to be; I spent hours exploring various services and this sort of idiocy is depressingly common. Shame on you, Internet.
An exceptional exception
Finally, an exception popped up. There is a Swiss online storage company,
MyDrive.ch, which offers a responsive, secure and well-priced service that supports WebDAV beautifully and has optional guest accounts. So, you can distribute the guest-account credentials and limit their access to specific folders and permissions. Perfect!

MyDrive even offers a free tier, with one guest account and 100MB of storage. That might be enough for many purposes, but I needed more storage than that. So I upgraded to their "MyDrive Pro" with over 3GB of storage for the princely sum of approximately $10 a year (and they gave me a bonus month on top of that). Additional guest accounts are $0.50 a month.
They have a free iOS app too, but that doesn't get around the problem that only Keynote can access your presentations on your iDevice. For that, we'll use WebDAV:
How to use MyDrive.ch's WebDAV feature to share your Keynote presentations
1) Set up your MyDrive.ch account in a browser on your computer or iPad. You'll receive an authentication email immediately; look for this, and click the activation link it contains. All set!
2) In the browser, log in and establish any folder structure you want. I suggest creating a dedicated folder for uploads from your guest(s) if that's something you might want to enable. MyDrive.ch enforces a rule that only the master account can write to the root folder; by default, guests can access files in the root folder for read-access only.
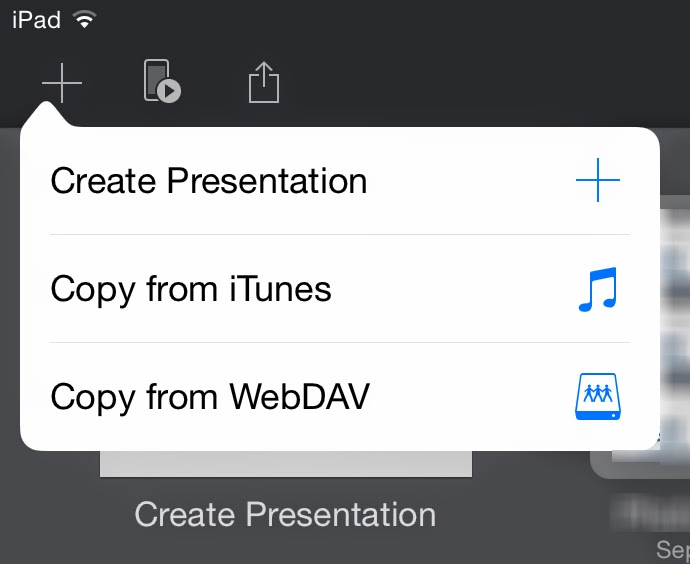
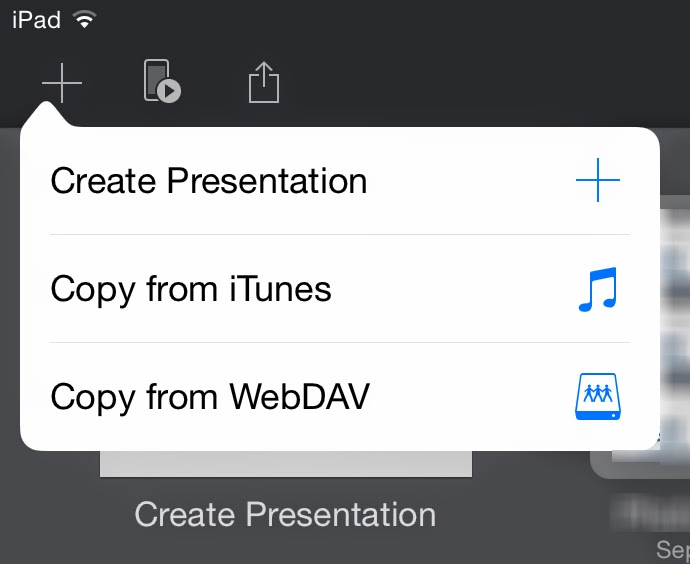
3) Switch to Keynote. On iOS, in order to log into your WebDAV-supporting service to upload a presentation, you must first go through the initial steps of downloading something even if there's nothing there yet to download. So to start: In Keynote's screen that presents your collection of presentations, click the "+" sign at the upper left, and select Copy from WebDAV. A login screen will appear.
4) For the URL, type https://webdav.mydrive.ch/ ...you can add a folder-name to that if you wish. (All this is case-sensitive.) Type in the user name you just established, or the guest name in the form of GuestName@MainUserName. Then, fill in the password for the user you just entered.

5) Click "Sign In." Your file-list, if any, will appear. Clicking on any presentation will download it to your iDevice's Keynote store. (Keynote files will show up with a .zip extension-- ignore that.)
6) To upload a presentation to share with others, cancel out of the login screen and open the presentation you want to upload. Click the Share button, then Send a Copy.) Select WebDAV. From the upload formats you're offered, you'll probably want to choose Keynote. Your iDevice will click and whirr for a moment, and then the file will be uploaded.
Done!
Steps 4 & 5 are all your colleagues need to access your presentations: they'd just click the "+" button at the top left of their Keynote presentations listing, Copy from WebDAV, fill in the URL and guest username and password, et voila.
A few caveats
MyDrive supports SSL encryption, as you may have noticed from the https URLs in these examples. However, if you want your browser-based connection encrypted, you must checkmark the "Use SSL encryption" option at the login screen, even if you logged in via https://mydrive.ch. I would prefer an "always use SSL" option be instituted in the account settings ...and certainly if you log in via an SSL-encrypted page, your connection should stay SSL-encrypted. From a usability standpoint, this is a minor but potentially important behavior to be aware-of. UPDATE: The responsive MyDrive folks have responded to this post by changing to an always-on SSL policy. Great!
If you wish to allow your colleagues to upload presentations without giving away your master account credentials:
- Create a folder to receive their uploads: Log into your MyDrive.ch account using a browser on your computer or iPad. Add the folder via the "Create Folder" button.
- Create a guest account for your colleagues to use and set its permissions to allow uploads: In the Settings menu, select the Guests tab. Create the guest account there, assigning full access to the guest. (
Currently, MyDrive's upload access setting doesn't actually enable uploading from within iWork applications via WebDAV. I have brought this bug to MyDrive.ch's attention.UPDATE: Per MyDrive's engineers, this behavior is probably due to Keynote's usage of temporary scratch files.) Don't worry, a guest account with "full access" can't delete files or folders at the root level. If you wish to restrict access to specific folders for specific guest accounts, use a browser to go to your main file listing, and click the permissions button to the right of the folder.

MyDrive.ch offers other goodies too. For example, you can mount your MyDrive store as a network drive if your operating system supports such things (and all versions of OS X have done so: In Finder's Go menu, select
Connect to Server and use the URL
https://webdav.mydrive.ch ...authenticating with your username and password.)
Recommended. My colleagues and I have already found this to be very useful for distributing some of my Greatest Hits presentations... and, likewise, getting their own to me, directly from their iPads.